Inprosec through its services, such as the SAP Security Assessment, helps its customers to improve the security levels of their SAP systems.
April 2021 notes
Summary and highlights of the month
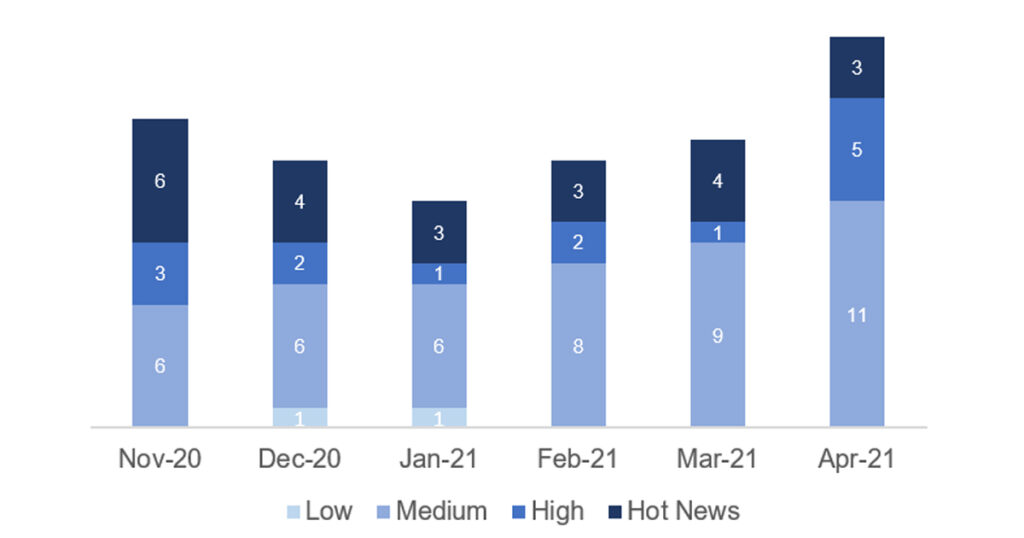
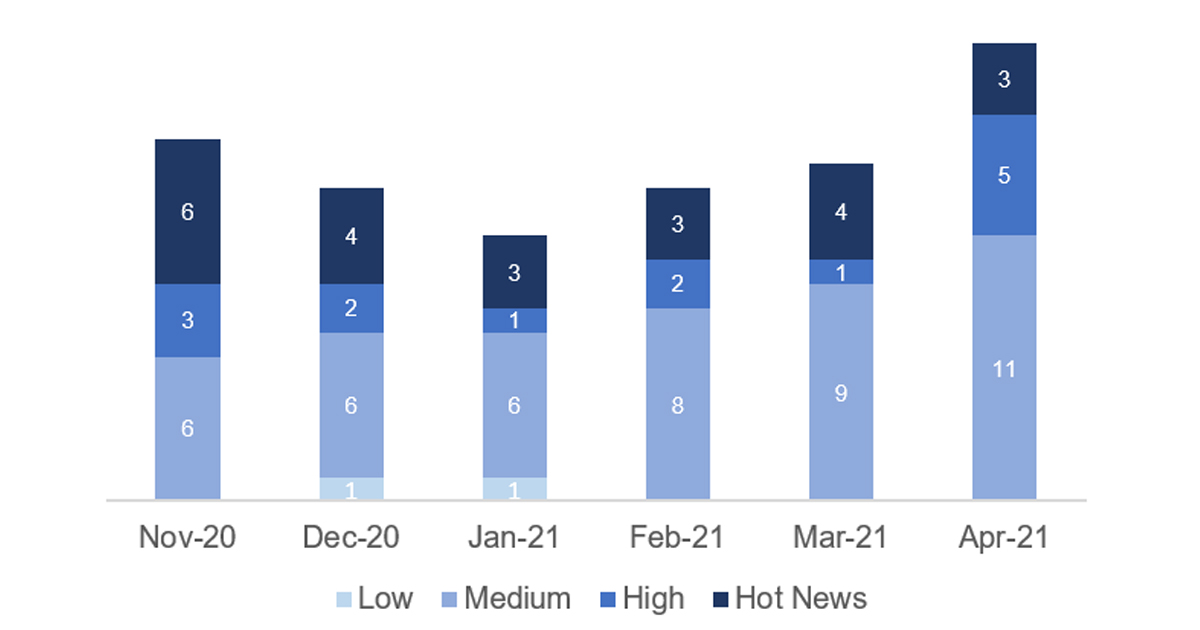
The total number of notes/patches has increased compared to last month. Despite this increase in the total number of notes, the number of Hot News has decreased, with 4 notes last month compared to 3 in April. On the other hand, it is worth noting the increase in the number of high criticality notes from 1 to 5 this month. As usual, we will leave the medium and low grades unreviewed this month, but we will give details of a total of 8 grades (all those with a CVSS of 7 or higher).
We have a total of 23 notes for the whole month, 5 more than last March (19 from Patch Tuesday, 14 new and 5 updates, being 6 notes more than last month).
We have one new Hot News, being the total of 3 in this month that stand out for their high CVVS, one of them the recurring update for the SAP Business Client with Chromium. In addition we will review in detail the high notes of this month (with a CVSS greater than 7), which are a total of 5.
- The most critical note of the month (with CVSS 10) is an upgrade. This note would be the usual “Browser Control Google Chromium Delivered with SAP Business Client”.
- Next in criticality (with CVSS 9.9 and 9.6) is a Code Injection Vulnerability affecting SAP Commerce and the other a Missing Authorization Check affecting SAP NetWeaver AS JAVA (MigrationService).
- From there, we located a total of 5 notes of high priority, highlighting one with a CVSS of 8.3, being a new note of possible obtaining passwords through the brute force method in the administrative accounts of SAP NetWeaver Master Data Management.
- This month the most prevalent types are “Information Disclosure” (6/23 and 5/19 on patch day) and “Missing Authorization Check” (4/23 and 4/19 on patch day).
In the graph (post April 2021 from SAP) we can see the classification of the April notes in addition to the evolution and classification of the last 5 previous months (only the notes of Sec. Tuesday / Patch Day – by SAP):
Full details
The full details of the most relevant notes are as follows:
- Update – Security updates for the browser control Google Chromium delivered with SAP Business Client (2622660): This security note addresses multiple vulnerabilities in the 3rd party web browser control Chromium, which can be used within SAP Business Client. This note will be modified periodically based on web browser updates by the open source project Chromium. The note priority is based on the highest CVSS score of all the vulnerabilities fixed in the latest browser release. CVSS v3 Base Score: 10 / 10.
- Remote Code Execution vulnerability in Source Rules of SAP Commerce (3040210): SAP Commerce Backoffice application allows certain authorized users to create source rules which are translated to drools rule when published to certain modules within the application. An attacker with this authorization can inject malicious code in the source rules and perform remote code execution enabling them to compromise the confidentiality, integrity and availability of the application. SAP Commerce Cloud addresses this vulnerability by adding validation and output encoding when processing Promotion Rules and other Source Rules. CVSS v3 Base Score: 9.9 / 10 (CVE-2021-27602).
- Update – Missing Authorization Check in SAP NetWeaver AS JAVA (Migration Service) (3022422): The MigrationService, which is part of SAP NetWeaver, does not perform an authorization check. This might allow an unauthorized attacker to access configuration objects, including such that grant administrative privileges. This could result in complete compromise of system confidentiality, integrity, and availability. Аs a final solution, you have to patch your systems with a new version of the J2EE-APPS.SCA, which is proided in the attached correction measures. The correction adds the missing authorization check. Keep in mind that this solution is an offline deployment that requires a restart of your systems. CVSS v3 Base Score: 9.6 / 10 (CVE-2021-21481).
- Information Disclosure in SAP NetWeaver Master Data Management (3017908): When security guidelines and recommendations concerning administrative accounts of a SAP NetWeaver Master Data Management installation have not been thoroughly reviewed, a malicious user with access to the MDM Server subnet might try to find the password using a bruteforce method. If successsful, the attacker could obtain access to highly sensitive data and MDM administrative privileges. The solution is to apply the latest patch, effectively replacing the main server executable and restarting it. In addition, the use of strong password should be enforced, especially for administrative accounts. It is highly recommended to create an additional administrative user in addition to the default ‘Admin’ account, in order to alleviate the possible locking of this default account. CVSS v3 Base Score: 8.3 / 10 (CVE-2021-21482).
- Information Disclosure in SAP Solution Manager (3017823): Under certain conditions SAP Solution Manager allows a high privileged attacker to get access to sensitive information which has a direct serious impact beyond the exploitable component. Some impacts of Information Disclosure could be the loss of information and system configuration confidentiality or information gathering for further exploits and attacks. The solution would be to implement the attached correction instructions in the note or install the corresponding Support Package. After you do so, the information will no longer be disclosed. CVSS v3 Base Score: 8.2 / 10 (CVE-2021-21483).
- Update – Missing Authorization check in SAP NetWeaver AS ABAP and SAP S4 HANA (SAP Landscape Transformation) (2993132): SAP Landscape Transformation allows a high privileged user to execute a RFC function module to which access should be restricted. This weakness gives attacker ability to read some sensitive internal information and also make vulnerable SAP systems completely unavailable. To solve the problem, the affected RFC function module have now been enforced to properly check access restrictions and it is necessary to implement the attached correction instructions in this security note. CVSS v3 Base Score: 7.6 / 10 (CVE-2020-26832).
- Unquoted Search Path in SAPSetup (3039649): An unquoted service path in SAPSetup could lead to privilege escalation during the installation process that is performed when an executable file is registered. This could further lead to complete compromise of confidentiality, Integrity and Availability. To fix this issue, a new process has now been created with a quoted path to the executable. In order to apply the fix, update NwSapSetup to a version 9.0.107.0 or higher from Software downloads available in the SAP Support Portal. There is no impact on functionality after the fix. CVSS v3 Base Score: 7.5 / 10 (CVE-2021-27608).
- Information Disclosure in SAP NetWeaver AS for Java (Telnet Commands) (3001824): An Unauthorized attacker may be able to entice an administrator to invoke telnet commands of an SAP NetWeaver Application Server for Java that allow the attacker to gain NTLM hashes of a privileged user. The vulnerability is a result of SMB relay attack. This correction prevents usage of SMB protocol. To fix the issue apply the corrective measure according to the “Validity” and “Support Packages & Patches” sections of the note. CVSS v3 Base Score: 7.4 / 10 (CVE-2021-21485).
Reference links
Reference links of the CERT of the INCIBE in relation to the publication of the notes for April:
https://www.incibe-cert.es/alerta-temprana/avisos-seguridad/actualizacion-seguridad-sap-abril-2021
Other references, from SAP and Onapsis (April):
https://wiki.scn.sap.com/wiki/pages/viewpage.action?pageId=573801649
Resources affected
- SAP Business Client, versión 6.5;
- SAP Commerce, versiones 1808, 1811, 1905, 2005 y 2011;
- SAP Fiori Apps 2.0 for Travel Management in SAP ERP, versión 608;
- SAP Focused RUN, versiones 200 y 300;
- SAP Manufacturing Execution, versiones 15.1, 15.2, 15.3 y 15.4;
- SAP NetWeaver:
- Master Data Management, versiones 710 y 710.750;
- AS for ABAP, versiones 2011_1_620, 2011_1_640, 2011_1_700, 2011_1_710, 2011_1_730, 2011_1_731 y 2011_1_752, 2020, 731, 740, 750 y 7.30;
- SAP NetWeaver Application Server Java (Applications based on Web Dynpro Java), versiones 7.00, 7.10, 7.11, 7.20, 7.30, 731, 7.40 y 7.50;
- SAP Netweaver AS JAVA (Applications based on HTMLB for Java), versiones:
- EP-BASIS, versiones 7.10, 7.11, 7.30, 7.31, 7.40 y 7.50;
- FRAMEWORK, versiones 7.10 y 7.11;
- FRAMEWORK-EXT , versiones 7.30, 7.31, 7.40 y 7.50;
- SAP Netweaver AS JAVA (Customer Usage Provisioning Servlet), versiones 7.31, 7.40 y 7.50;
- SAP NetWeaver AS JAVA (HTTP Service), versiones 7.10, 7.11, 7.20, 7.30, 7.31, 7.40 y 7.50;
- SAP NetWeaver AS JAVA (MigrationService), versiones 7.10, 7.11, 7.30, 7.31, 7.40 y 7.50;
- SAP NetWeaver AS JAVA (Telnet Commands), versiones:
- ENGINEAPI, versiones 7.30, 7.31, 7.40 y 7.50;
- ESP_FRAMEWORK, versiones 7.10, 7.20, 7.30, 7.31, 7.40 y 7.50;
- J2EE-FRMW, versiones 7.10, 7.20, 7.30, 7.31, 7.40 y 7.50;
- SERVERCORE, versiones 7.10, 7.11, 7.20, 7.30, 7.31, 7.40 y 7.50;
- SAP Process Integration, versiones 7.10, 7.20, 7.30, 7.31, 7.40 y 7.50;
- SAP S4 HANA (SAP Landscape Transformation) , versiones 101, 102, 103, 104 y 105;
- SAP Setup, versión 9.0;
- SAP Solution Manager versión 7.2;