Inprosec a través de sus servicios, como el SAP Security Assessment, ayuda a sus clientes a mejorar los niveles de seguridad de sus sistemas SAP.
Notas Septiembre 2022
Resumen y highlights del Mes
El número total de notas/parches ha sido de 16, 5 más que el mes pasado. El número de Hot News se mantiene, habiendo una, igual que el mes de agosto. Por otro lado, cabe destacar que aumentan el número de notas de criticidad alta pasando de 3 a 6 en este mes. Como siempre dejaremos las notas medias y bajas sin revisar en este mes, pero daremos detalle de un total de 7 notas (todas las que tengan un CVSS de 7 o mayor).
Tenemos un total de 16 notas para todo el mes, 5 notas más que el pasado agosto (las 13 del patch Tuesday, 8 nuevas y 5 actualizaciones, son 5 notas más que el pasado mes).
Revisaremos en detalle 7 del total de 7 notas altas y Hot News, siendo la Hot News una actualización de una nota anterior y las 2 de 6 notas altas serían nuevas (aquellas de CVSS mayor o igual a 7).
- La nota más crítica del mes (con CVSS 10) es la habitual nota relacionada con «Google Chromium».
- La siguientes en criticidad (CVSS 8,8, 8,1, 7,8, 7,8, 7,7 y 7,1) son seis notas altas, una de «Cross-Site Scripting (XSS) vulnerability in SAP Knowledge Warehouse”, otra relacionada con “Privilege escalation vulnerability” en SAP SuccessFactors, otra estaría relacionada con “Windows Unquoted Service Path” en la plataforma SAP Business, otra relacionada “Central Management Server Information Disclosure”, otra relacionada con “Privilege escalation vulnerability” en SAP BusinessObjects Business Intelligence Platform (CMC) y la última estaría relacionada con “Insufficient Firefighter Session Expiration” en SAP Access Control
- El resto (9) son de nivel medio y bajo, y no las veremos en detalle.
- Este mes los tipos más predominantes son “Cross-Site Scripting (XSS) vulnerability » (4/16 y 4/13 en patch day) e “Information Disclosure vulnerability” (4/16 y 2/13 en patch day).
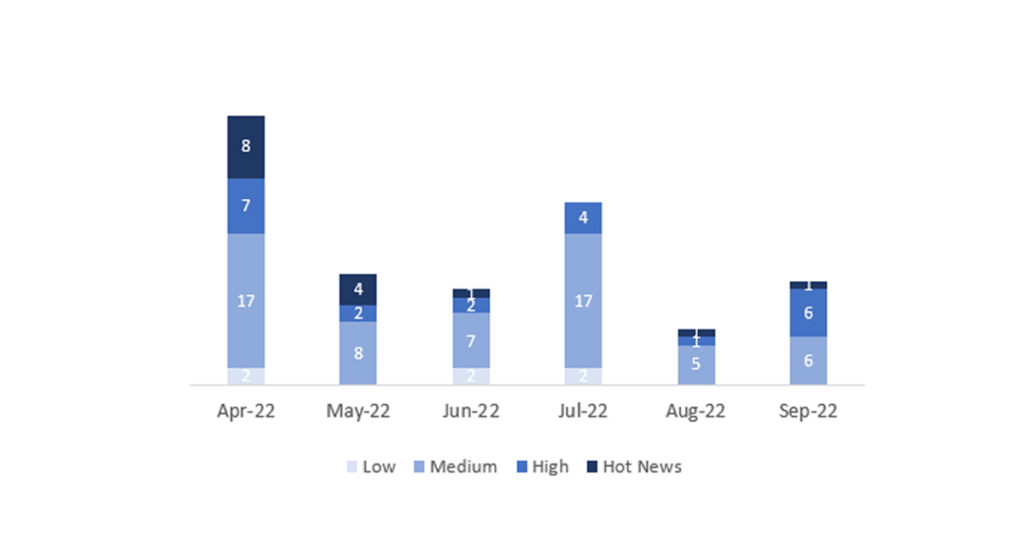
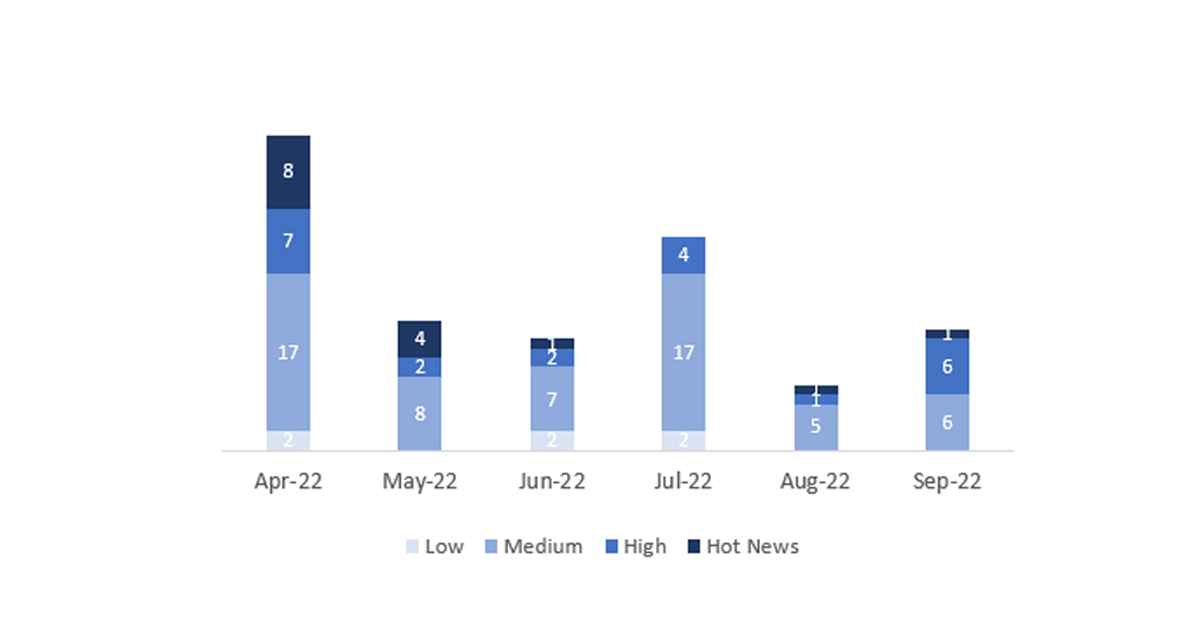
En la gráfica (post agosto 2022 de SAP) podemos ver la clasificación de las notas de septiembre además de la evolución y clasificación de los últimos 5 meses anteriores (solo las notas del Sec. Tuesday / Patch Day – by SAP):
Detalle completo
El detalle completo de las notas más relevantes es el siguiente (en inglés):
- Update – Security updates for the browser control Google Chromium delivered with SAP Business Client (2622660): This security note addresses multiple vulnerabilities in the 3rd party web browser control Chromium, which can be used within SAP Business Client. This note will be modified periodically based on web browser updates by the open-source project Chromium. The note priority is based on the highest CVSS score of all the vulnerabilities fixed in the latest browser release. If the SAP Business Client release is not updated to the latest patch level, displaying web pages in SAP Business Client via this open-source browser control might lead to different vulnerabilities like memory corruption, Information Disclosure and the like. The solution will be to update the SAP Business Client patch to the newest one, which contains the most current stable major release of the Chromium browser control, which passed the SAP internal quality measurements of SAP Business Client. CVSS v3 Base Score: 10 / 10 (Multiple CVE´s).
- Update – Cross-Site Scripting (XSS) vulnerability in SAP Knowledge Warehouse_(3102769): This security note addresses a vulnerability that has been discovered in the SAP Knowledge Warehouse (SAP KW). The use of an SAP KW component within a web browser allows unauthorized attackers to carry out XSS attacks, which could lead to the disclosure of sensitive data. The SAP KW display component does not sufficiently validate and encode the input parameters, resulting in a reflected cross-site scripting issue. To fix the problem, the procedure would be as follows: Deploy the support packages and patches referenced in this SAP release. Workaround: In case you are unable to implement the patch, you have two options to fix the issue, which are described in SAP Note 3221696 «Disabling SAP IKS component». CVSS v3.0 Base Score: 8,8 / 10 (CVE-2021-42063).
- Update – Privilege escalation vulnerability in SAP SuccessFactors attachment API for Mobile Application(Android & iOS) (3226411): Due to misconfigured application endpoints, SAP SuccessFactors attachment APIs allow an attacker with user privileges to perform activities with admin privileges over the network. These APIs were consumed in the SF Mobile application for Time Off, Time Sheet, EC Workflow and Benefits. On successful exploitation, the attacker can read/write attachments, compromising the confidentiality and integrity of the application. Customers using attachments in Time Off, Time Sheet, EC Workflow and Benefits modules of SAP SF Mobile Application are impacted. Several measures have been taken to resolve the identified vulnerability in the most recent software update. This vulnerability impacts users who are using the iOS and Android mobile application versions released previous to V8.0.5. For this reason, the SAP SuccessFactors mobile team is releasing an immediate fix to stop the ability to download, upload or preview attachments from the impacted SAP SF Mobile modules at this time. To fix the issue, download the latest version of the SAP SuccessFactors iOS and Android mobile application (V8.0.5) to ensure the organization is not at risk of any threats from this vulnerability. CVSS v3 Base Score: 8,1 / 10 (CVE-2022-35291).
- Windows Unquoted Service Path issue in SAP Business One (3223392): In SAP Business One application when a service is created, the executable path contains spaces and isn’t enclosed within quotes, leading to a vulnerability known as Unquoted Service Path which allows a user to gain SYSTEM privileges. If the service is exploited by adversaries, it can be used to gain privileged permissions on a system or network leading to high impact on Confidentiality, Integrity and Availability. To fix the problem, Customer need upgrade to SAP Business One FP2202HF1. CVSS v3 Base Score: 7.8 / 10 (CVE-2022-35292).
- Update – Central Management Server Information Disclosure in Business Intelligence Update (2998510): During an update of SAP BusinessObjects Enterprise, Central Management Server (CMS) authentication credentials are being exposed in Sysmon event logs. This Information Disclosure could cause a high impact on systems’ Confidentiality, Integrity, and Availability. To fix this problem, apply the patches contained in the «Support Package Patches» section. CVSS v3 Base Score: 7.8 / 10 (CVE-2022-28214).
- Information Disclosure vulnerability in SAPBusinessObjects Business Intelligence Platform (CMC) (3217303): Under certain conditions Central Management Console (CMC) allows an attacker to access certain unencrypted sensitive parameters which would otherwise be restricted. To fix this problem, apply the patches contained in the «Support Package Patches» section. CVSS v3 Base Score: 7.7 / 10 (CVE-2022-39014).
- Insufficient Firefighter Session Expiration in SAP GRC Access Control Emergency Access Management (3237075): SAP GRC Access control Emergency Access Management allows an authenticated attacker to access a Firefighter session even after it is closed in Firefighter Logon Pad. This attack can be launched only within the firewall. On successful exploitation the attacker can gain access to admin session and completely compromise the application. To solve this issue, implement the correction statement for all plugin systems, where Web Based Firefighter is used. With this fix, the Firefighter session will be detected using SM04 and SM05 information. To correctly retrieve the SM05 data, the RFC user must have the following authorization object assigned: ‘S_ADMI_FCD’, ID: ‘S_ADMI_FCD’ and field: ‘PADM’. The minimum version required to apply the fix is SAP NetWeaver Enhancement Package 2 for 7.0 Support Package Stack 00. Below this level, the fix has no effect and we suggest you upgrade your SAP Basis level. CVSS v3 Base Score: 7.1 / 10 (CVE-2022-39801).
Enlaces de referencia
Otras referencias, en inglés de SAP y Onapsis (septiembre):
https://dam.sap.com/mac/app/e/pdf/preview/embed/ucQrx6G?ltr=a&rc=10
SAP Security Patch Day September 2022 (onapsis.com)
Recursos afectados
El listado completo de los sistemas/componentes afectados es el siguiente:
- SAP Access Control, Version – 12
- SAP Business Client, Versions – 6.5, 7.0, 7.70
- SAP Business One, Versions – 10.0
- SAP BusinessObjects Business Intelligence Platform (CMC), Versions – 430
- SAP BusinessObjects Business Intelligence Platform, Versions – 420, 430
- SAP Knowledge Warehouse, Versions – 7.30, 7.31, 7.40, 7.50
- SAP SuccessFactors attachment API for Mobile Application(Android & iOS), Versions <8.0.5