Inprosec a través de sus servicios, como el SAP Security Assessment, ayuda a sus clientes a mejorar los niveles de seguridad de sus sistemas SAP.
Notas Julio 2022
Resumen y highlights del Mes
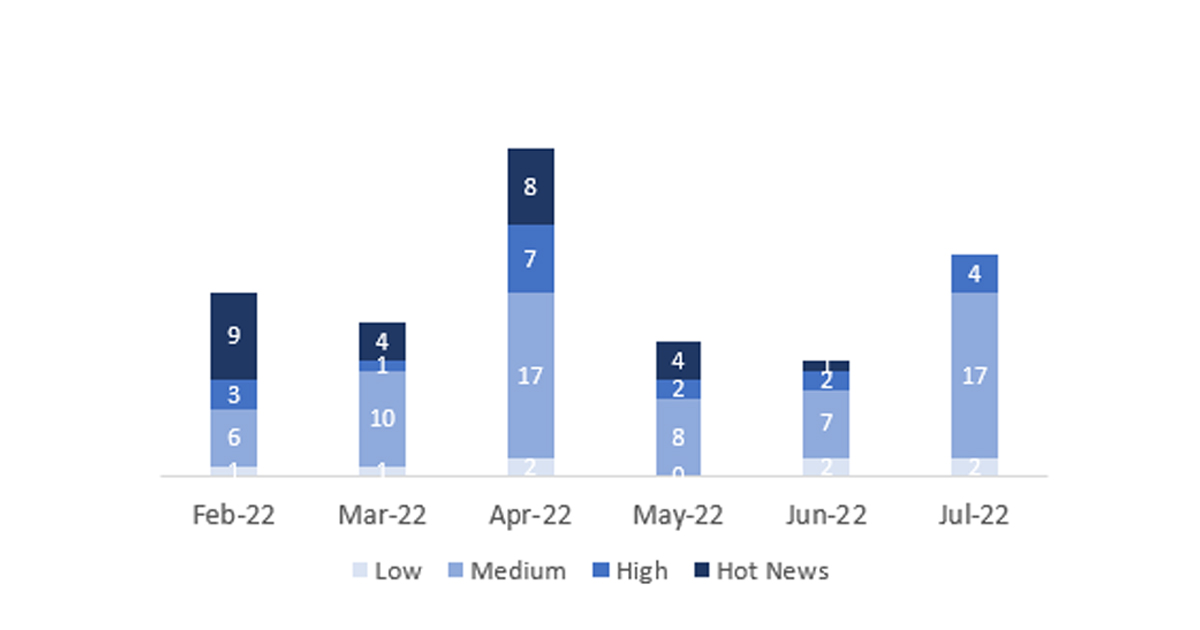
El número total de notas/parches ha sido de 27, 10 más que el mes pasado, a pesar de un mayor número de notas, el número de Hot News disminuyen, siendo 1 la que encontrábamos el mes pasado, no habiendo ninguna existente en julio. Por otro lado, cabe destacar, que aumentan el número de notas de criticidad alta pasando de 3 a 5 en este mes. Como siempre dejaremos las notas medias y bajas sin revisar en este mes, pero daremos detalle de un total de 5 notas (todas las que tengan un CVSS de 7 o mayor).
Tenemos un total de 27 notas para todo el mes, 10 notas más que el pasado Junio (Las 23 del patch Tuesday, 20 nuevas y 3 actualizaciones, 11 notas más que el pasado mes).
Revisaremos en detalle 5 del total de 5 notas altas nuevas (aquellas de CVSS mayor o igual a 7).
- Las nota más alta del mes (con CVSS 8,3) es la “Information disclosure vulnerability in SAP BusinessObjects Business Intelligence Platform (Central management console)”
- La siguientes en criticidad (CVSS 7,6, 7,5 , 7,4 y 7,4) son cuatro notas altas, una de «Information Disclosure vulnerability in SAP Business One”, otra relacionada con “Missing Authentication check in SAP Business One (License serviceAPI)”, otra relacionada con “Code Injection vulnerability in SAP Business One» y la última se trata de una actualización relacionada con “Improper Access Control check in SAP NetWeaver basicadmin and adminadapter services”.
- El resto (22) son de nivel medio y bajo, y no las veremos en detalle, aunque cabe destacar que hay más de una que afecta a SAP NetWeaver.
- Este mes los tipos más predominantes son “Cross-Site Scripting (XSS) vulnerability» (7/27 y 7/23 en patch day) y “Missing Authorization Check” (5/27 y 3/23 en patch day).
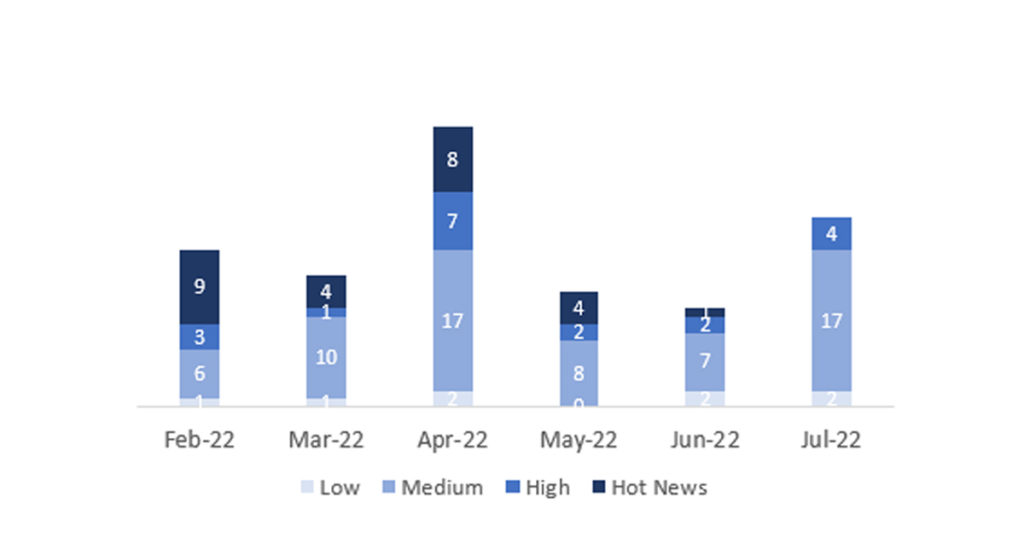
En la gráfica (post Julio 2022 de SAP) podemos ver la clasificación de las notas de julio además de la evolución y clasificación de los últimos 5 meses anteriores (solo las notas del Sec. Tuesday / Patch Day – by SAP):
Detalle completo
- Information disclosure vulnerability in SAP BusinessObjects Business Intelligence Platform (Central management console) (3221288): SAP BusinessObjects CMC allows an unauthenticated attacker to retrieve token information over the network which would otherwise be restricted. This can be achieved only when a legitimate user accesses the application and a local compromise occurs, like sniffing or social engineering. On successful exploitation, the attacker can completely compromise the application. Taken care of hiding token.This is fixed in all available code lines. 4.2 SP09 Patch 9, 4.3 SP01 and above releases. CVSS v3 Base Score: 8,3 / 10 (CVE-2022-35228).
- Information Disclosure vulnerability in SAP Business One (3212997): Under special integration scenario of SAP Business one and SAP HANA, an attacker can exploit HANA cockpit’s data volume to gain access to highly sensitive information. The note offers a workaround, use Explicit Password instead of XPAth Password in FTP Adapter. For other parts, customer need upgrade B1. CVSS v3 Base Score: 7,6 / 10 (CVE-2022-32249).
- Missing Authentication check in SAP Business One (License service API) (3157613): Due to missing authentication check, SAP Business one allows an unauthenticated attacker to send malicious http requests over the network. On successful exploitation, an attacker can break the whole application making it inaccessible.To solve this issue, customers should upgrade to SAP Business One 10.0 FP2202. For SAP customers who cannot apply the corresponding patch immediately, the note refers to knowledge base article 3189816 for a temporary workaround describing how to prevent end users from accessing the license API. CVSS v3 Base Score: 7,5 / 10.
- Code Injection vulnerability in SAP Business One (31911012): SAP BusinessObjects CMC allows an unauthenticated attacker to retrieve token information over the network which would otherwise be restricted. This can be achieved only when a legitimate user accesses the application and a local compromise occurs, like sniffing or social engineering. On successful exploitation, the attacker can completely compromise the application. CVSS v3 Base Score: 7.4 / 10 (CVE-2022-31593).
- Update – Improper Access Control check in SAP NetWeaver basicadmin and adminadapter services (3147498): Improper Access Control is detected in SAP NetWeaver AS Java, basicadmin and adminadapter services remote objects are not properly protected. As a result, some administrative functionalities are exposed to public access, which means the Availability could be impacted. This correction discontinues public access to basicadmin and adminadapter services remote objects by introducing required authentication and authorization protection. To solve the issue, please apply the corrective measure according to the «Support Packages & Patches» section of the note. CVSS v3 Base Score: 7.4 / 10
Enlaces de referencia
Otras referencias, en inglés de SAP y Onapsis (julio):
https://dam.sap.com/mac/app/e/pdf/preview/embed/ucQrx6G?ltr=a&rc=10
https://onapsis.com/blog/sap-security-patch-day-july-2022-three-applications-focus
Recursos afectados
El listado completo de los sistemas/componentes afectados es el siguiente:
- SAP Adaptive Server Enterprise (ASE),Version -KERNEL 7.22, 7.49, 7.53, KRNL64NUC 7.22, 7.22EXT, 7.49, KRNL64UC 7.22, 7.22EXT, 7.49, 7.53
- SAP Business Objects, Version -420
- SAP Business One License serviceAPI, Version -10.0
- SAP Business One, Version -10.0
- SAP BusinessObjects Business Intelligence Platform (Central management console),Versions -420, 430
- SAP BusinessObjects Business Intelligence Platform (LCM),Versions -420, 430
- SAP BusinessObjects Business Intelligence Platform (Visual Difference Application),Versions -420, 430
- SAP BusinessObjects Business Intelligence Platform 4.x,Versions -420, 430
- SAP BusinessObjects BW Publisher Service, Versions -420,430
- SAP Enterprise Extension Defense Forces & Public Security (EA-DFPS),Versions -605, 606, 616,617,618, 802, 803, 804, 805, 806
- SAP Enterprise Portal, Versions -7.10, 7.11, 7.20, 7.30, 7.31, 7.40, 7.50
- SAP NetWeaver Application Server for ABAP and ABAP Platform,Versions -700, 701, 702, 710, 711, 730, 731, 740, 750, 751, 752, 753, 754, 755, 756, 787, 788
- SAP NetWeaver Enterprise Portal (WPC), Versions -7.30, 7.31, 7.40, 7.50
- SAP NetWeaver Enterprise Portal, Versions -7.10, 7.11, 7.20, 7.30, 7.31, 7.40, 7.5
- SAP3D Visual Enterprise Viewer, Version -9.0
- SAPS/4HANA(Supplier Factsheet and Enterprise Search for Business Partner, Supplier and Customer),Versions -104, 105, 106
- SAPS/4HANA, Versions -101, 102, 103, 104, 105, 106
- SAPS/4HANA, Versions -S4CORE 101, 102, 103, 104, 105, 106, SAPSCORE 127