Inprosec through its services, such as the SAP Security Assessment, helps its customers to improve the security levels of their SAP systems.
November 2022 notes
Summary and highlights of the month
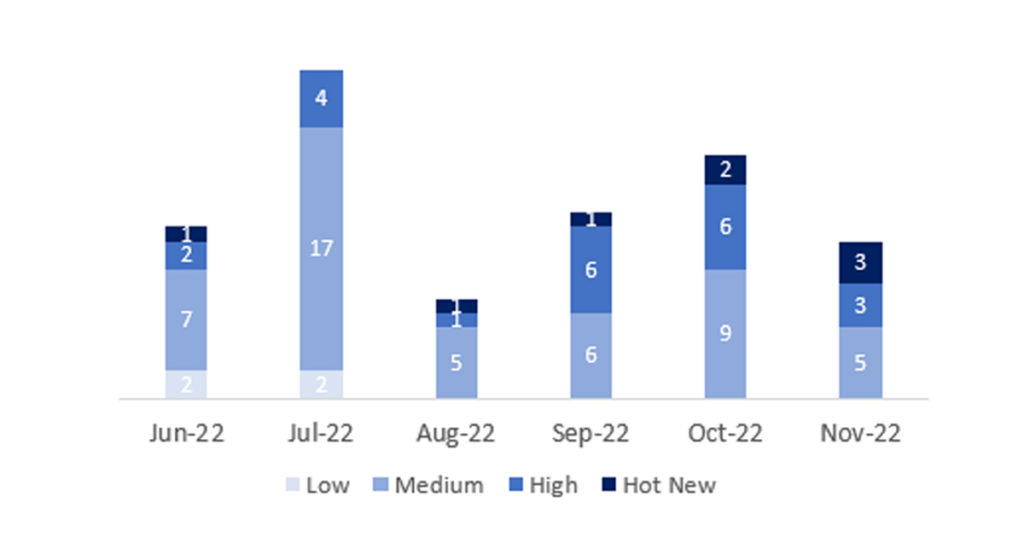
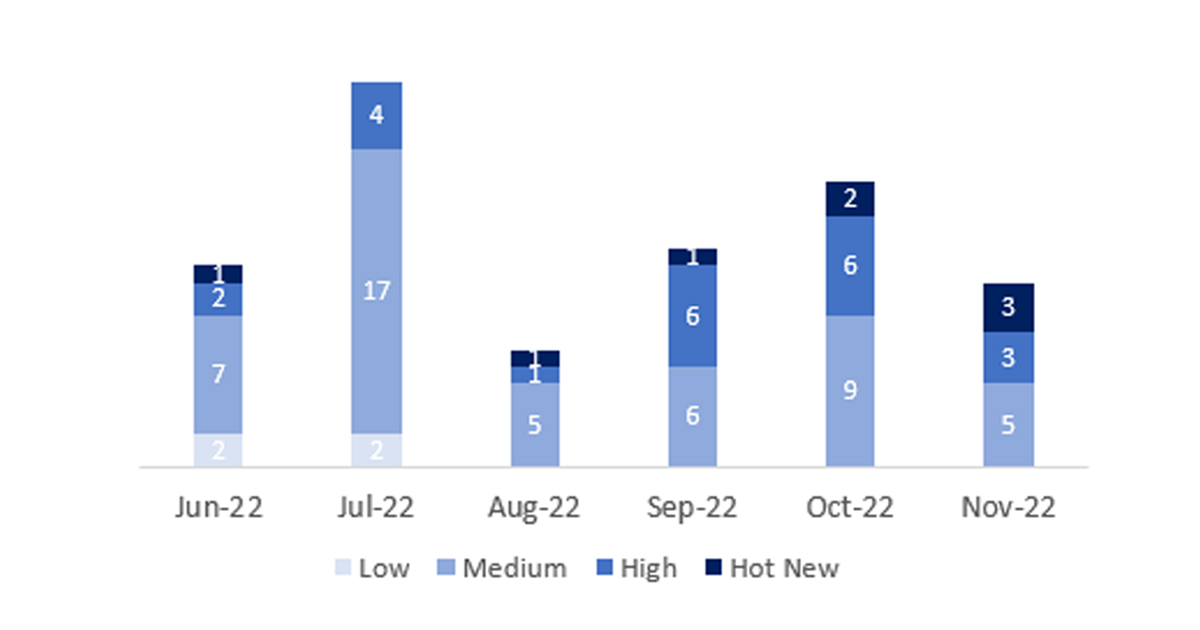
The total number of notes/patches was 14, 8 less than last month. The number of Hot News increased from 2 to 4 this month. On the other hand, it is worth noting that the number of high criticality notes decreases this month from 6 to 3. As usual we will leave the medium and low notes unchecked this month, but we will give details of a total of 7 notes (all those with a CVSS of 7 or higher).
We have a total of 14 notes for the whole month (the 11 from Patch Tuesday, 9 new and 2 updates, that’s 6 notes less than last month).
We will review in detail 7 of the total 7 high notes and HotNews, 2 of the 4 HotNews are new and 5 of 6 high notes would be new (those of CVSS greater than or equal to 7).
- The most critical note of the month (with CVSS 10) is the usual note related to “Google Chromium”.
- The next in criticality (CVSS 9.9) would be another HotNews, related to “Insecure Deserialization of Untrusted Data in SAP BusinessObjects Business Intelligence Platform (Central Management Console and BI Launchpad)”.
- Next in criticality (CVSS 9,8) another HotNews, related to “Multiple Vulnerabilities in SQlite bundled with SAPUI5“.
- The next one is another HotNews (CVSS 9,6), it is an update of the note related to “Account hijacking through URL Redirection vulnerability in SAP Commerce login form”.
- The next in criticality (CVSS 8.7, 8.1, and 7.0) are three high notes, one of “Multiple vulnerabilities in SAP NetWeaver Application Server ABAP and ABAP Platform”, the next is an update of a note released in July, “Privilege escalation vulnerability in SAP SuccessFactors attachment API for Mobile Application(Android & iOS)” and the last one would be related to “Arbitrary Code Execution vulnerability in SAP 3D Visual Enterprise Author and SAP 3D Visual Enterprise Viewer”.
- This month the most predominant type is “Cross-Site Scripting (XSS)” (2/14 and 1/11 in patch day).
Full details
The complete detail of the most relevant notes is as follows:
- Update – Security updates for the browser control Google Chromium delivered with SAP Business Client (2622660): This security note addresses multiple vulnerabilities in the 3rd party web browser control Chromium, which can be used within SAP Business Client. This note will be modified periodically based on web browser updates by the open source project Chromium. The note priority is based on the highest CVSS score of all the vulnerabilities fixed in the latest browser release. If the SAP Business Client release is not updated to the latest patch level, displaying web pages in SAP Business Client via this open source browser control might lead to different vulnerabilities like memory corruption, Information Disclosure and the like. The solution will be to update the SAP Business Client patch to the newest one, which contains the most current stable major release of the Chromium browser control, which passed the SAP internal quality measurements of SAP Business Client. CVSS v3 Base Score: 10 / 10 (Multiple CVE´s).
- Insecure Deserialization of Untrusted Data in SAP BusinessObjects Business Intelligence Platform (Central Management Console and BI Launchpad) (3243924): There is no verification in the de-serialization process, in some workflow of SAP BusinessObjects BI Platform (Central Management Console and BI LaunchPad), an authenticated attacker with low privileges can intercept a serialized object in the parameters and substitute with malicious serialized one, which leads to deserialization of untrusted data vulnerability. CVSS v3 Base Score: 9,9 / 10 [CVE-2022-41203].
- Multiple Vulnerabilities in SQlite bundled with SAPUI5 (3249990): An issue was found in fts5UnicodeTokenize() in ext/fts5/fts5_tokenize.c in Sqlite. A unicode61 tokenizer configured to treat unicode “control-characters” (class Cc), was treating embedded nul characters as tokens. SAPUI5 framework is using SQLite < 3.34.0 which was treating null characters as tokens, this could be exploited by an user over the network having low privileges leading to considerable impact on confidentiality, integrity and availability of applications using SAPUI5. . CVSS v3 Base Score: 9,8 / 10 [CVE-2021-20223].
- Update – Account hijacking through URL Redirection vulnerability in SAP Commerce login form( 3239152): An attacker can change the content of an SAP Commerce login page through a manipulated URL. They can inject code that allows them to redirect submissions from the affected login form to their own server. This allows them to steal credentials and hijack accounts. A successful attack could compromise the Confidentiality, Integrity, and Availability of the system. This is due to multiple URLs on the SAP Commerce OAuth extension login page not being sanitized. This allowed attackers to construct manipulated URLs to the login page that would change the behaviour of the login form. In particular, login credentials would be redirected from the SAP Commerce server to an arbitrary server on the Internet. CVSS v3.0 Base Score: 9,6 / 10 [CVE-2022-41204]
- Multiple vulnerabilities in SAP NetWeaver Application Server ABAP and ABAP Platform (3256571): Due to insufficient input validation, SAP NetWeaver Application Server ABAP and ABAP Platform allows an attacker with high level privileges to use a remote enabled function to delete a file which is otherwise restricted. On successful exploitation an attacker can completely compromise the integrity and availability of the application. CVSS v3 Base Score: 8,7 / 10 (CVE-2022-41214).
- Update – Privilege escalation vulnerability in SAP SuccessFactors attachmentAPIfor Mobile Application(Android &iOS) (3226411): Due to misconfigured application endpoints, SAP SuccessFactors attachment APIs allow an attacker with user privileges to perform activities with admin privileges over the network. These APIs were consumed in the SF Mobile application for Time Off, Time Sheet, EC Workflow and Benefits. On successful exploitation, the attacker can read/write attachments, compromising the confidentiality and integrity of the application. Customers using attachments in Time Off, Time Sheet, EC Workflow and Benefits modules of SAP SF Mobile Application are impacted. Several measures have been taken to resolve the identified vulnerability in the most recent software update. This vulnerability impacts users who are using the iOS and Android mobile application versions released previous to V8.0.5. For this reason, the SAP SuccessFactors mobile team is releasing an immediate fix to stop the ability to download, upload or preview attachments from the impacted SAP SF Mobile modules at this time. To fix the issue, download the latest version of the SAP SuccessFactors iOS and Android mobile application (V8.0.5) to ensure the organization is not at risk of any threats from this vulnerability. CVSS v3 Base Score: 8,1 / 10 (CVE-2022-35291).
- Arbitrary Code Execution vulnerability in SAP 3D Visual Enterprise Author and SAP 3D Visual Enterprise Viewer (3263436): SAP SQL Anywhere and SAP IQ database servers are vulnerable to a remote unauthenticated stack-based buffer overflow when the server is running with a server debugging option. Impacts of stack-based buffer overflow are, read and modify unauthorized data. Vulnerability has a direct impact on availability of a system. CVSS v3 Base Score: 7.0 / 10 [CVE-2022-41211]
Reference links
Other references, from SAP and Onapsis (November):
https://dam.sap.com/mac/app/e/pdf/preview/embed/ucQrx6G?ltr=a&rc=10
SAP Patch Day: November 2022 (onapsis.com)
Resources affected
- SAP 3D Visual Enterprise Author,Version –9.0
- SAP 3D Visual Enterprise Viewer,Version –9.0
- SAP BusinessObjects Business Intelligence Platform (Central Management Console and BI Launchpad), Versions -4.2, 4.3
- SAP Commerce, Versions -1905, 2005, 2105, 2011, 2205
- SAP NetWeaver Application Server ABAP and ABAP Platform,Versions-700, 731, 804, 740, 750, 789
- SAP SuccessFactors attachmentAPIfor Mobile Application(Android &iOS), Versions -<8.1.2
- SAPUI5 CLIENT RUNTIME, Versions –600, 700, 800, 900, 1000
- SAPUI5, Versions –754, 755, 756, 757